Installing TLS Certificates
TLS certificates (updated, more secure, version of SSL) are necessary to enable secure HTTPS connections between a browser and your application. These certificates can be bought online, or generated by Clever Cloud. In that case, we manage the whole process for you.
There is two ways to get HTTPS for your apps:
- Let’s Encrypt: Provided by default by Clever Cloud. Free. Nothing to configure.
- Your own certificates: If you already have a certificate, you can upload it securely.
Getting Certificates with Let’s Encrypt
Clever Cloud automatically generates and renews TLS certificates for your domains. To enable this:
- Add your domain to the application:
- Use the Console or
- Use clever-tools
- Configure your DNS records to point to Clever Cloud’s load balancers
Alternative Options
Immediate Certificate Coverage
To avoid any period without certificate coverage (e.g., during migration from another provider):
- Upload your existing certificate first
- Let Clever Cloud generate a new certificate automatically when your uploaded one expires
Wildcard Certificates
Clever Cloud’s automatic certificate generation doesn’t support wildcard certificates. For wildcard certificates, you can:
- Generate your own Let’s Encrypt certificate
- Purchase a commercial certificate
- Contact support for a quote on managed certificate services
Need immediate certificate generation? Contact the support team for manual activation.
Cloudflare configuration
If you use Cloudflare to manage your domain, the certificate generation could fail depending on your SSL/TLS settings, you will encounter 502 HTTP errors if Cloudflare expects SSL/TLS strict mode and automatically redirects to HTTPS.
To prevent this from happening you can create a page rule to bypass this policy as Let’s Encrypt needs to access the route /.well-known/acme-challenge* via HTTP to generate the certificate:
Define a page rule
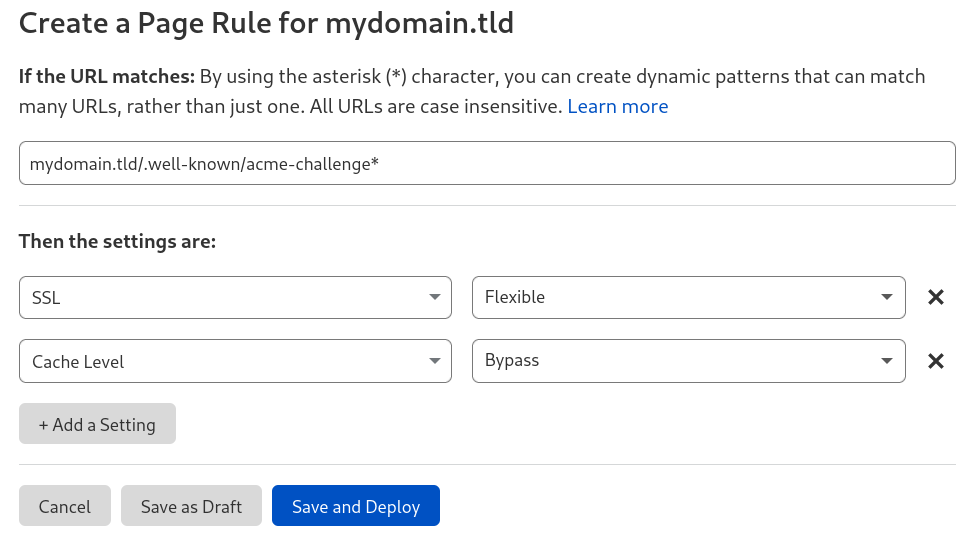
We also recommend to disable the cache level.
Turn off HTTP to HTTPS redirection on Cloudflare
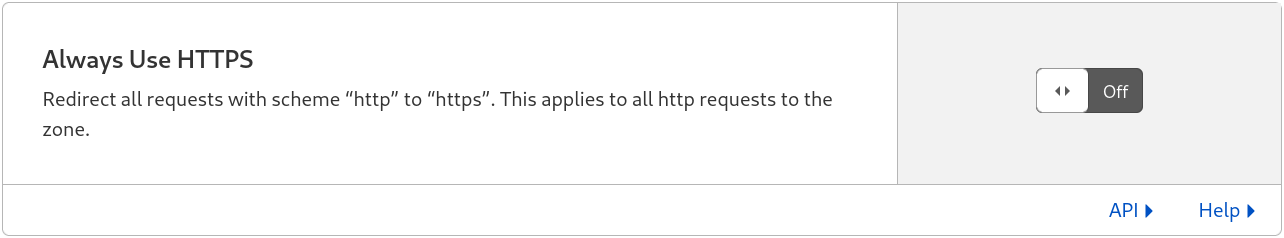
You can enable Force HTTPS in the information tab of your Clever Cloud application instead.
$ curl http://<your-domain>/.well-known/acme-challenge/test
testIt should return a HTTP 200 OK with the string “test” as the body. If it does not, check your Cloudflare configuration.
Uploading my own certificates
You can upload certificates yourself: https://api.clever-cloud.com/v2/certificates/new ↗
Prerequisites
You need to paste a PEM bundle containing (in this order):
- the private key
- the certificate itself
- intermediate certificates (optional)
You should create a file.pem containing:
-----BEGIN PRIVATE KEY-----
<the private key>
-----END PRIVATE KEY-----
-----BEGIN CERTIFICATE-----
<the certificate>
-----END CERTIFICATE-----You may need to mention the algorithm in the footer and header.
For instance, if the previous format doesn’t work, try to use
-----BEGIN RSA PRIVATE KEY----- and -----END RSA PRIVATE KEY-----
You can add optionnal intermediate certificates by appending them to the file as
-----BEGIN CERTIFICATE-----
<the certificate>
-----END CERTIFICATE-----You should note that `.pem`` files use the unix way of terminating lines with a single line feed character. Make sure your text editor does the same.
Certificate Submission Checklist
You .pem file must be correctly formatted to successfully upload your certificate. This checklist might help you troubleshoot uncesuccessful certificate submission.
| Certificate Specifications |
|---|
| ✅ The private key is included |
| ✅ Keys lenght are RSA and either 2048 or 4096 |
| ✅ ECDSA is not used to create your certificate |
| ✅ The line feed (LF) characters at the end |
| ✅ The certificate chain include your certificate together with all the intermediary CA certificates that signed it, in that order |
Sending Certificates Manually
In the event that you request the installation of a certificate by the support team, this operation will be charged on a one-off basis for each request. Please contact us for installation rates.
Sharing Certificates via Keybase
Another way to transmit your certificates is Keybase. Keybase is an encrypted social networking service providing a key directory that maps social media identities to encryption keys (including, but not limited to PGP keys) in a publicly auditable manner. Additionally it offers an end-to-end encrypted chat, you can use to share sensitive informations, such as SSL/TLS certificates.
If your are a Keybase.io user, you can find us at keybase.io/clevercloud.
Sharing Certificates via GPG
Email can be a secure way to transfer your certificates when using a signed and encrypted email with GPG. Our dedicated email for receiving certificates is ssl@clever-cloud.com.
- fingerprint:
0394 3517 934C 1FA5 ED4E 2F61 218B 86BD 5278 460F - 64-bit:
218B 86BD 5278 460F
-----BEGIN PGP PUBLIC KEY BLOCK-----
mQINBFa4bJMBEAC21vsfJ1ay5iVUcKsP8X8GziZu8daV5G4Lqpns54zN/GB05f9+
3jV1RYRMweq7RC6XU/GDZo20ksvDw0N963/WCswCt0MyzM1O105tZ/ZbYyVV/w5w
763DXCUPdBhzcA7o31A7JgPimiceP/BcyA8CniLSD4nfzD0CiM74kdG5/vx2Ve9T
vkJ0wX5qWFvEivBPf/+jUfmdwtx5RLjH783xRuh0wWcz9ey/hsuLxJmdDuIlUccu
yH0itAMiLmI0yGscTVQ6pmLmEY1GZY3GSrTZbDOrKbJLxPjtRAtW8JvE1UD9AOqs
yvJ+QYp+6viEkQg0Fq2agCkpWTEy/6INGvjwexHkq9zUBe/Dm0awcqg46GSY8cwA
gqaaV32hPwv4fYMsz8fH50DDIAmKjJspWTeehnaXUSmr9lHpYH/l1mHPOtCvBL2e
m52YAKF5bCQEwn1p/UsysxtTaOrLO3ZoRTpM9lAeR3SfM768lnLzpI2AcpyJ95jg
btibuy59WvCQMdbA6UneaWxaOhSAtAB3OzHauXhQzru1BXfy5VOva5YHgH+4xS9n
7aqMxG0uB9X7wcPPV9FHFv+6QnKZ1fHLf6zN0tUjoXTIS6egbJqtYcTbDE8nRgoU
rwEadolEVSNnTEX3cfdueUHslMZwF+U30RG2bHSJTmUTOnVT6g1zk2hxwwARAQAB
tD5DbGV2ZXIgQ2xvdWQgKENsZXZlciBDbG91ZCdzIFNTTCBlbWFpbCkgPHNzbEBj
bGV2ZXItY2xvdWQuY29tPokCVAQTAQoAPgIbAwULCQgHAwUVCgkICwUWAgMBAAIe
AQIXgBYhBAOUNReTTB+l7U4vYSGLhr1SeEYPBQJp8aObBQkmBToIAAoJECGLhr1S
eEYPUQkP/jp3PrQmKmu91SJrnor0tt81TKhNWWvbeNs6yxMtB0YujvtFb1BzY9Pb
bLxDbjuh2JKroRzZVDVR4I3YfDVX4OMqrc6PdOlCg6k3UFfOHN7dknzc+tAGxjrC
vaJ6TyvrLAUyWBNfXeWLxANgZJpjPn5xFMG8HzZKbiXvmNP4jUXyS6mzZH6tS/KM
GlPmlLw3hrnHpCFqRAxjUdXA5qrCXwQJW+61Etwjq9xgf3J+qaUkaTGpv+0KxvG3
d3Jmamh/ROXLJDa97JQbdxej5U5CtDXNf+G+rC7PD0zpfukdhOpzhY5nT7bcg6c9
xLCev8kaKyy1AEujOSDs9BbRbWSuR21iuOYJlo83zQXK8IG9rnwk1Lfilkkm7QuW
KxntqqzTWo6aWHYgsEzUkh096kaL13R/Q+n9E/rULtXxAgCbkjZVgpcC3Bs0bnEI
PGAaz1kmN1l0b301Gh5WWWr/wcBEYE4DMmvReqm5mziFqa6K9gfw7VzJ92N+6Obq
zWQGX93cPpclotAJBcMMF3RPEsEqxGUMLRSGUakUmb4lVvrPxoAmh7lFO0EM43NL
5h9SgXzQm7R1OmclGESTCSIuEoNtKhrz8LOot+vGlZEi+9dwoFjXS9JAv7uGdXCs
ns5Waspk+gebsVn77NgCAdtas1Hsq7/lMHdEQdP6UwQLUuWF50lriQIcBBABCAAG
BQJXM7fEAAoJEHV4qTsu8rd9PyQP/A7tQ03KDb/Se01zBYK/8vVhqkyMgGTAqRgy
ctngaR4oVRKAUlxVr4zflhiJ93lQOaK9lParx8uSkpmOsKrqHD3zH1/RorjynVlY
4yS2w+Hh6iG+M/A6mAlKEYdyJdunM+5/V/2j97it6ZfAazK+XX0tUlqnT1ECnkp7
FlUJ90Zq//yFYAytUWgzUJI16D7OsVh8K5Z+t8h7+ovaUY96DaPj34cwHECeCCob
fZct+DNTbVfhc6qGKZOjTcpJkwLPC7q3dNlWW2XESF7qit7ZPcEuvaHFjBva45Js
+5Fa57O23iK2WjQG0QDNGahu8hT9Xr3DlIw1ptzkHa9kbVzKhHPju+ka6STmq4Hm
ygv3lgkL5wG4BBBKeTsl8cxGWa3y5q2EmtjssgF+DnY0MBlUDwpKn/6SkQ4a6rxj
U88C7neWdttjIbdqq1SfVwa2IkJ2lfrcEPqRtJZDrvUaa9d/WYdI5U20OPEIYaMN
5sj9/BOnO309eTwzOnsMjTHlN6rwuDa1SGkuVpEYmLW4dY/57LfjJRUiN+61H6el
a8kJgGDtTFqnx78ohPXfo920wAnPzG7AcuXr9qVoU010okb22XZEECRgn35WVoiU
8Cr1fAu0nydN4nzAm2F9y58N7lIagqzMTEwRy4CqAZoiTD9fl/hwCMQ8WpTq4nDR
4MJvK1ERuQINBFa4bJMBEACnZ8sIzvuuYRETK3hGfY+x35FToB3iTlmW6DokTQEL
0ffjREqjdWJdXbnxiqDatryuv1qcnipf5PlmyBVDp1pGy0TuX013rbD7zplwj5q/
edwAoCKFmy5l5mIjg2V0IWholS7YjG38GTimlj5SjQyR0vdGr/qkS3hYaM6b4oxj
fyZJgaDOR3I6udxnz5djxQW/Nr8wC7i6S526H66jNdG8KJp6ITHg6E9HhOSxnpGs
/75/9nLBN/X1Cff/uJyRbhNTsX+SEYyD7G1OSAUD6l16zYmt+AUbvO8sixCp8Hus
1M08dpCFrN1ANZf3KXOD4DP+6gXecxwSAt1rCbZfrRzLOjSiC3UXV/6O4y8kn5bt
qjsN+97SqhJC0Q6aZHyxzi9UHN08AUI6HxBiqbXPgkZsNyZZ8bjKkZsFcGIYvJ4l
GbejiJEGQCXuORI0l4Oc7hqOtOZlhKk7815xtYCLJsjGmipDdjLfpfJMkmnqyJ7/
oFYQX60lQLjDiNCK4Z4T4Cz1XCQaewfT6b2A7CI79NShyvE4dqVbYYHqz1XbMGow
UcTApmAZlcswbshuIdLvZCevKfBmmQBbfbxJRv8OCQjkNtt5UMa0U0cEOKrEWBES
/tzwOmeckrtZfn0cBmVcNzPWN9zqgoIUgsMHS6N+5x5EwYLFnuZKWSndweJsS+xb
XwARAQABiQI8BBgBCgAmAhsMFiEEA5Q1F5NMH6XtTi9hIYuGvVJ4Rg8FAmnxo7QF
CSYFOiEACgkQIYuGvVJ4Rg/VchAAnI5G1RaxFHIR3qoETB9J7+csWcC2AzfArKxR
BdSNKXldX2CnJmy5Ak3AJk6ooT2XjUjcRswa87ab2h+MtQB0sKwcab2Wm8rr/WQa
cB+lPQgqSHt8rTlM2UnN3B1aki9POggFH+Ca2NXDuENgx/9yn6O+FB53ReM4wfBN
AHvpczXy5evP9e/Rql3xsst2RkXe4FCQmqQv/c1fiDqw14opFakvfeW8cFvElTwz
JQprDOzcXlyhgHRe5w48fONUXxQJ3FDBmEnyIWoVpQJfgzJz68QUvuTtqvz7+6fF
zf+dV0t6b1nLMXHqU4lPfACvzYpHGb3ef/v+JtDX2CR6k3MAcoK6pmthU4ArgoHP
qfwpGum/gkk2nk3tHuocEx6dR2I91eQr7YDvN4T9Om16Wzd06tpywqjd/Pw0OU9L
x829vaiLuAg2Z+eZDNMzcjg75UeblocNsRrkXMZ9/TvGrZvILGBg4DpT7nRwM3WL
Qo62kLZM73utzgwXCuNozFu18LV9ppW9WvF/rgAyR6YVoIkK31B+GQc7oqMTVcve
CzbZqzKOkq3Kni2yfGu6V/TGrq2LDc0eqy7xB5LYOI+00Y5+nRKbpOjt6M9y4W3u
if9+g4cSnL6+w1HCLrohnHvrIsnfYKdZm86VcZ9r9JRnC2Re9fGWOMsWIh1PKdil
SboMCws=
=VOPS
-----END PGP PUBLIC KEY BLOCK-----Managed Certificate Service
If you cannot provide your own certificates or prefer not to manage the certificate lifecycle yourself, Clever Cloud can handle certificate procurement and management on your behalf. This service covers wildcard certificates and cases where automatic Let’s Encrypt generation isn’t suitable.
Service Overview
Clever Cloud manages the entire certificate lifecycle:
- Certificate generation and procurement
- Domain validation coordination
- Initial installation
- Renewal management
Information Required
To initiate a managed certificate request, contact our support team with:
- Validity duration: Certificate validity period (default: 1 year)
- Protected domains: Domain(s) requiring certificate coverage (one domain per certificate is recommended)
Domain Validation
Certificate authorities require proof of domain ownership before issuing certificates. You must complete validation using one of two methods:
Email Validation
The certificate authority sends a validation email to one of these addresses on your domain:
admin@yourdomain.comadministrator@yourdomain.comwebmaster@yourdomain.comhostmaster@yourdomain.compostmaster@yourdomain.com
At least one of these addresses must be functional. You’ll receive an email containing a validation link that you must click to confirm domain ownership.
DNS Validation
If email validation isn’t possible, you can validate via DNS:
- Clever Cloud provides either a TXT or CNAME record value
- Create the record (TXT or CNAME) in your domain’s DNS zone
- Validation completes automatically once the record propagates
Installation and Renewal
After successful validation:
- The certificate is generated and installed on your application
- Clever Cloud monitors certificate expiration
- Several weeks before expiry, the support will contact you to initiate renewal
- The validation and installation process repeats
For pricing and to initiate a managed certificate request, contact the support team.
Did this documentation help you ?